General
Zero-day attacks: protection against the invisible?
Zero Day protection: Protecting against the invisible?
The digital landscape is evolving at breakneck speed - and with every new development New dangers on. Zero-day attacks on Windows users currently pose a particularly serious risk. But what exactly is behind this phenomenon and what exactly does zero-day protection look like?
- Zero day attacks - an overview
- Zero Day protection: how can you protect yourself?
- Examples of known zero-day attacks
- Conclusion on zero day protection
Zero day attacks - an overview
What are zero-day attacks?
Zero-day attacks affect security vulnerabilities that unknown to the developers are. These vulnerabilities are not yet covered by security updates, which gives attackers a dangerous head start. The term „zero-day“ makes it clear that the developers had zero days to fix the problem - the attackers exploit these gaps before countermeasures can even be developed.
But how dangerous are such attacks really? The answer is simple: Extremely threatening. Since there are no ready-made defenses, attackers can penetrate systems unhindered. This type of attack is comparable to an invisible burglar who robs your company while you are asleep. You only notice the damage afterwards.
The current threat situation
 In recent months, Windows users around the world have fallen victim to a wave of zero-day attacks. These targeted previously unknown vulnerabilities in Windows operating systems and caused considerable damage: From data loss to Operational failures up to massive financial losses companies from a wide range of sectors have felt the consequences.
In recent months, Windows users around the world have fallen victim to a wave of zero-day attacks. These targeted previously unknown vulnerabilities in Windows operating systems and caused considerable damage: From data loss to Operational failures up to massive financial losses companies from a wide range of sectors have felt the consequences.
It is becoming increasingly clear that zero-day attacks are a growing problem. They are the invisible thieves of the digital world, targeting unprotected systems while you go about your work unsuspectingly.
How does Zero Day work?
Attackers exploit security vulnerabilities in the software to inject malicious code. This code can take a wide variety of forms, from malware that steals confidential data, up to and including ransomware, that paralyzes systems and makes ransom demands. This malware is often spread via infected emails, manipulated websites or compromised files.
An impressive example of this is the WannaCry ransomware attack This attack exploited vulnerabilities in the Windows operating system and was launched in 2017. infected thousands of computers worldwide. The damage was in the billions.
Would you like to switch?
Save now with our SME offers
- Save up to 40% now
- Latest technology
- Simple changeover & easy operation
Zero Day: How can you protect yourself?
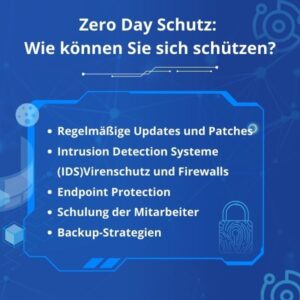 Effective protection against zero-day attacks requires a comprehensive security approach that covers different layers. Here are five essential measures you should take:
Effective protection against zero-day attacks requires a comprehensive security approach that covers different layers. Here are five essential measures you should take:
- Regular updates and patches: Make sure that all your software is always up to date. Many attacks exploit known vulnerabilities that can be closed by updates.
- Intrusion Detection Systems (IDS): These systems monitor network traffic and can identify suspicious behavior that indicates a zero-day attack.
- Endpoint Protection: Modern security solutions offer Comprehensive protection for your end devices and can detect and block suspicious activity before damage occurs.
- Training of employees: Security awareness is a key factor. Your employees should be regularly trained to recognize phishing attacks and handle emails and files securely.
- Backup strategies: Regular backups of your data minimize the risk of data loss and enable rapid recovery in the event of an attack.
Examples of known zero-day attacks
It is useful to take a look at some prominent zero-day attacks of the past to illustrate the urgency of the issue. These examples impressively demonstrate how serious the consequences of such attacks can be:
1. stuxnet (2010)
The Stuxnet worm exploited several zero-day vulnerabilities in the Windows operating system to specifically attack industrial control systems. In particular Iranian nuclear facilities were hit, resulting in considerable physical damage to centrifuges. Stuxnet impressively demonstrated that zero-day attacks not only cause virtual damage, but can also destroy physical infrastructure.
2. heartbleed (2014)
The Heartbleed bug in the OpenSSL software enabled attackers to steal sensitive data such as Passwords and private keys from the memory from servers. Although Heartbleed was not technically a classic zero-day vulnerability, the gap was exploited undetected for a long period of time before a patch was available. The incident demonstrated the global impact of such vulnerabilities and highlighted the importance of proactive security measures.
3rd Google Chrome Zero-Day (2019)
A zero-day vulnerability in the Google Chrome browser allowed attackers to execute arbitrary code via manipulated websites on affected systems. This incident made it clear that even widespread software such as Chrome can be vulnerable to zero-day attacks.
4. Microsoft Exchange Server (2021)
In March 2021, critical zero-day vulnerabilities were discovered in Microsoft Exchange servers and exploited by a hacker group. Attackers penetrated thousands of company networks, took over e-mail accounts and installed malware. The far-reaching effects of this attack show how vulnerable even large companies are to zero-day threats.
Conclusion on zero day protection
Zero-day attacks are among the most dangerous threats in today's digital world. They are insidious and difficult to defend against because they exploit unknown vulnerabilities. But your company can protect itself by being proactive: Regular updates, comprehensive security solutions and well-trained employees are key to minimizing the risks. Remember: in cyber security Prevention is the most effective protection. Always stay one step ahead of the attackers and ensure that your company remains well armed - so that it can continue to focus on the essentials: success.
Would you like to switch?
Save now with our SME offers
- Save up to 40% now
- Latest technology
- Simple changeover & easy operation