- 22. Mai 2017
- Veröffentlicht durch: Admin
- Kategorie: Allgemein
In March 2017, KrebsOnSecurity warned that thieves who perpetrate tax refund fraud with the U.S. Internal Revenue Service were leveraging a widely-used online student loan tool to find critical data on consumers that allows them to claim huge refunds with the IRS in someone else’s name. This week, it emerged that a Louisiana-based private investigator is being charged with using the same online tool to glean tax data on then-presidential candidate Donald J. Trump.
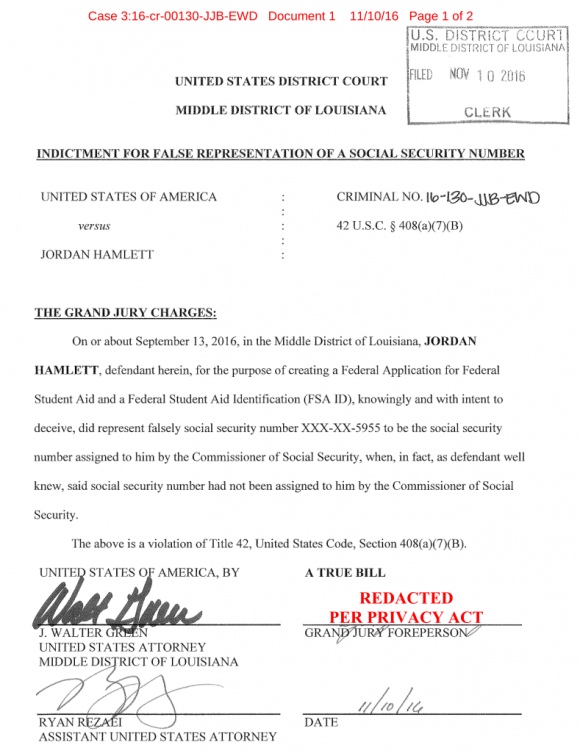
A story today at Diverseeducation.com points to court filings in the U.S. District Court for the Middle District of Louisiana, in which local private eye Jordan Hamlett is accused by federal prosecutors of abusing an automated tool at the U.S. Department of Education website that is designed to make it easier for families to complete the Education Department’s Free Application for Federal Student Aid (FAFSA) — a lengthy form that serves as the starting point for students seeking federal financial assistance to pay for college or career school.
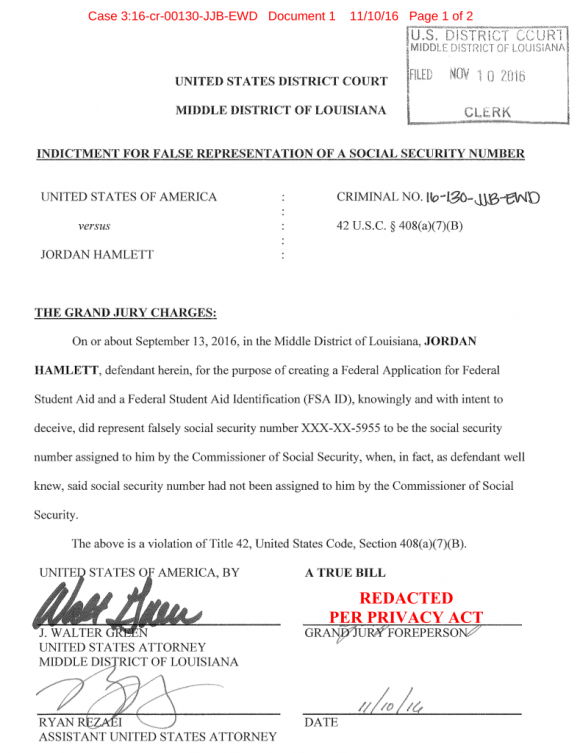
Grand jury findings in a sealed case against Louisiana private investigator Jordan Hamlett.
In November 2016, Hamlett — the owner of Baton Rouge-based Averlock Investigations — was indicted on felony charges of trying to glean then President-Elect Trump’s “adjusted gross income,” or AGI, using the FAFSA online tool. In the United States, the AGI is an individual’s total gross income minus specific deductions. Diverse Education’s Jamaal Abdul-Alim cites sources saying the accused may have been trying to get Trump’s tax records.
In any event, he failed, according to prosecutors. Last month, the IRS announced that the Education Department was disabling the FAFSA lookup tool because it was being abused by tax fraudsters.
According to Diverse Education, hints about the case against Hamlett came out earlier this month in an IRS oversight hearing before the U.S. House committee on oversight and government reform. At that hearing, “Timothy P. Camus, deputy inspector general for investigations at the Treasury Inspector General for Tax Administration, or TIGTA, alluded to the Hamlett case but did not mention Hamlett by name, nor did he indicate that then-presidential candidate Trump was the target,” Abdul-Alim writes. “Instead, Camus only mentioned that TIGTA ‘detected an attempted access to the AGI of a prominent individual.’”
Attempts to reach Hamlett for comment have been unsuccessful so far, and the complaint against him remains sealed. However, KrebsOnSecurity obtained a response on Nov. 10, 2016 from U.S. Attorney J. Walter Green that lays out the basic facts in the case. A copy of that document is here (PDF).
It’s interesting to note that this wasn’t the only time U.S. government authorities detected someone trying to access Trump’s AGI information. According to the government’s response, the alleged unauthorized attempt at Trump’s AGI data being attributed to Hamlett occurred on Sept. 13, 2016.
In TIGTA Deputy Inspector General Camus’ testimony to the House committee (PDF), he said his office detected a second attempt to access the same “prominent individual’s” AGI data via the FAFSA online lookup in November 2016, although the testimony doesn’t say whether that attempt was successful.
Amazingly, it wasn’t until an IRS employee on February 27, 2017 complained that his personal data was stolen via the FAFSA tool that the IRS moved to restrict online access to the service, according to response to committee questioning from IRS Chief Information Officer S. Gina Garza.
The government doesn’t say in its pleadings why the accused was allegedly unsuccessful in obtaining President Trump’s AGI data. It could be that the Social Security number he had for Trump wasn’t correct; or, the account may have been flagged prior to the alleged attempt.
In any event, I want to take this opportunity to remind readers to assume that the static facts about who you are — including your income, date of birth, Social Security number, and a whole host of other information you may consider private — are likely at risk thanks to well-intentioned but nonetheless poorly secured third-party services that leak this data if the impersonator has but a few data points with which to work.
And of course these data points are for sale via a myriad places in the Dark Web for less than the Bitcoin equivalent of a regular coffee at Starbucks. On this front I’m reminded of the case of ssndob[dot]ru, a now-defunct identity theft service that held this data on more than 200 million Americans.
That service was used to look up the name, address, previous address, phone number, Social Security number and date of birth on some of America’s top public figures and celebrities — data that was later published on a doxing site called exposed[dot]su. The victims of exposed[dot]su included then First Lady Michelle Obama; then-director of the FBI Robert Mueller; an former U.S. Attorney General Eric Holder.
![Exposed[dot]su was built with the help of identity information obtained and/or stolen from ssndob[dot]ru.](https://krebsonsecurity.com/wp-content/uploads/2014/03/exposed-su-600x462.png)
Exposed[dot]su was built with the help of identity information obtained and/or stolen from ssndob[dot]ru.
Source: Krebsonsecurity


