General
Endpoint Security explained
Endpoint security basics, definition and reliable protection measures
Today, cyber security is at the forefront of every company's agenda. Endpoint security is no longer just an optional extra, but an absolute necessity. This is because cyber attacks are on the rise. Attacks are directed against a wide range of end devices - from state-of-the-art smartphones to networked office devices. It is therefore essential that companies develop a robust defense strategy. In this article, we dive into the world of endpoint security. We highlight key concepts and show how companies can protect their most critical assets in an ever-changing threat environment.
Endpoint Security: What is it?
Endpoint security refers to a concept of cyber security. It aims to protect end devices such as desktops, laptops and mobile devices from malicious activities. According to the Definition of Gartner an endpoint protection platform (EPP) is a solution that is geared towards this,
- prevent attacks by file-based malware,
- recognize dangerous activities and
- initiate appropriate measures to investigate and rectify the situation.
What are end devices?
End devices can be stationary or mobile devices. The only important thing is that they are connected to the company network. Because any device, from a computer to a printer or even a coffee machine, can be such an endpoint.
- Computers, laptops, smartphones
- IoT (Internet of Things) devices such as modern refrigerators
- PoS systems (point-of-sale) such as cash registers or barcode scanners
- Infrastructure such as printers, switches, video surveillance, etc.
- All devices that are connected to the network.
Why is endpoint security important?
An endpoint security strategy is important because every single device potentially poses a threat to the entire network. The importance of endpoint security has increased significantly in recent years - especially due to increased home office use during and after the pandemic. A study by the ifo Institute from mid-2023 shows that home office use has stabilized at an average of 1.0 days per week. And according to Statista, 25% of employees were working from home at least part of the time in December 2022. This development has significantly increased the number of end devices that represent potential gateways for cyberattacks.
A 2023 from the Gothaer Insurance survey of 1023 participants revealed that 48% of companies perceive a hacker attack as the most threatening risk. This puts the fear of a cyber attack in first place among the greatest threats to SMEs for 5 years in a row.
According to Bitkom, data theft (customer data, industrial spies) accounts for 56% of attacks. In 2022, the types of attacks are as follows:
- 31% Phishing
- 29% Passwords
- 28% Malware
- 23% Ransomware
- 12% DDos attacks
According to Bitkom, the damage caused by cyber attacks has exceeded 200 billion euros for three years in a row since 2020. The risk of being attacked by entire groups is constantly increasing. In 2022, the proportion of major organized attacks by multiple perpetrators was over 60%. The origin of the attacks is also changing. According to Sinan Selen, Vice President of the Federal Office for the Protection of the Constitution More and more attacks from Russia or China.
Effective endpoint protection is crucial, as endpoints form the interface between man and machine. Companies are faced with the challenge of ensuring both security and not restricting the legitimate activities of their employees. Technical solutions can reduce the risk of social engineering attacks, but cannot completely eliminate them. In addition, newer developments such as the Internet of Things (IoT) and the increasing use of mobile devices in the business context call for ongoing adaptation and expansion of security strategies.
These facts underscore the importance of a robust endpoint security strategy that considers technical and human factors to effectively combat ever-evolving cyberthreats.
Would you like to switch?
Save now with our SME offers
- Save up to 40% now
- Latest technology
- Simple changeover & easy operation
How end device protection works
Endpoint security, also known as an endpoint protection platform (EPP), comprises centralized security systems that are used in companies to protect various endpoints - including servers, workstations, mobile devices and other workloads - from cyber threats. These systems scan files, processes and system activity to look for suspicious or malicious activity.
These solutions usually include a central management console. IT administrators are connected to the company network via this to monitor incidents, respond to them and take preventative measures. They can be implemented locally in a company's own data center, via cloud services or as a combination of both.
Traditional or „legacy“ solutions are based on a local security concept with a central data center as the core for security management. In this model, end devices are reached via an agent that provides security functions. A disadvantage of this model can be the creation of security silos, as management is often limited to the local network area.
With the trend towards working from home and the spread of BYOD (Bring Your Own Device) policies, many companies have switched to laptops and personal employee devices, highlighting the limitations of local security approaches. Some providers have therefore started to offer hybrid solutions that extend traditional architectures to include cloud capabilities.
Cloud-native solutions that have been specially developed for the cloud are a modern alternative. They enable administrators to monitor and manage end devices remotely via a cloud-based console. The agent installed on the end device establishes a connection to the console, but can also perform security tasks independently if there is no internet connection. These solutions use cloud control mechanisms and policies to extend security beyond the traditional network perimeter by breaking down silos and extending the administrator's reach.
Measures for the protection of endpoints
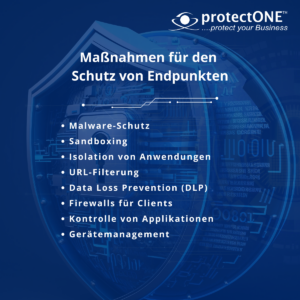 Approaches to endpoint security include not only technical but also organizational measures. These include, for example, employee training, guidelines for handling end devices and external storage media as well as raising awareness of different types of threats. When security providers talk about endpoint protection, they are usually referring to technical strategies. These usually include a combination of preventative, analytical and reactive elements. Typical technical measures for endpoint security include
Approaches to endpoint security include not only technical but also organizational measures. These include, for example, employee training, guidelines for handling end devices and external storage media as well as raising awareness of different types of threats. When security providers talk about endpoint protection, they are usually referring to technical strategies. These usually include a combination of preventative, analytical and reactive elements. Typical technical measures for endpoint security include
- Malware protection
- Sandboxing
- Isolation of applications
- URL filtering
- Data Loss Prevention (DLP)
- Firewalls for clients
- Control of applications
- Device management for external hard disks, USB sticks or Bluetooth components etc.
Comparison between endpoint protection and virus protection
Endpoint protection software provides comprehensive security measures for different types of devices - both physical and virtual, regardless of whether they are located in a data center or in the cloud. This type of software can be installed on a variety of devices such as laptops, desktop computers, servers, virtual machines and remote endpoints.
Antivirus programs are often a component of more comprehensive endpoint protection solutions and are generally considered a more basic form of protection. These programs focus primarily on identifying and removing known viruses and other types of malware, rather than using advanced methods such as threat detection and endpoint-based detection and response (EDR). Traditional antivirus programs work in the background and regularly scan the contents of a device to find matches to the signatures of known viruses in a database. They are typically installed on individual devices inside and outside the network firewall.
Would you like to switch?
Save now with our SME offers
- Save up to 40% now
- Latest technology
- Simple changeover & easy operation


